Recent Posts
You don’t have to look far to find inspiring examples of women’s achievement in the fraud industry, where parity in the field yields inspiring success stories across the board. Longtime Riskified partner and renowned fraud expert, Dajana Gajic-Fisic, is one such example. One of our 2023 Titans of Ecommerce award winners, Dajana received the Vision … Continued
Commonly known across the world as Chinese New Year, the 2026 Spring Festival ushers in the year of the Horse and with it, an unbridled surge in shopping and economic activity. But as consumer spending rises, so do the methods of those looking to exploit the holiday rush. How can ecommerce businesses protect themselves and … Continued
Is it romance, or is it risky business? For retailers, the Valentine’s Day rush brings a specific challenge: differentiating between a love-struck procrastinator and a fraudster capitalizing on the chaos. Last-minute spending and unfamiliar customer profiles elevate risk for brands eager to capture this revenue opportunity. And where there’s opportunity, fraud follows. Fraud loves a … Continued
In-store transactions are often perceived as lower risk compared to online card-not-present purchases. EMV chip cards, card-present authentication, and protections from card networks and processors create a sense of security that can make additional fraud tools appear unnecessary, expensive, or even disruptive to the checkout experience. What’s more, because effective fraud protection stops fraudulent transactions … Continued
Big sporting events like the Super Bowl don’t just drive fan excitement and spending — they also create prime conditions for ecommerce fraud. Tickets can be purchased almost instantly with limited identity data, traffic spikes strain traditional payment reviews, and high-demand tickets are easy to resell across a wide range of secondary marketplace platforms. When … Continued
Are merchant teams stuck in “AI tourism”? This week at the RILA CEO Forum 2026 in Ojai, CA, Bret Taylor CEO of Sierra shared a provocative point of view: top-down AI mandates from boards and CEOs may actually have slowed AI adoption. Under pressure from leadership, middle management is engaging in what Bret framed as … Continued
It feels like every week brings a new headline or article about innovations in agentic commerce. As we move toward a world where AI agents conduct commerce at scale, clearly understanding the risks introduced becomes critical. One of the primary risks is the loss of key transaction signals used for fraud detection. Categories of data … Continued
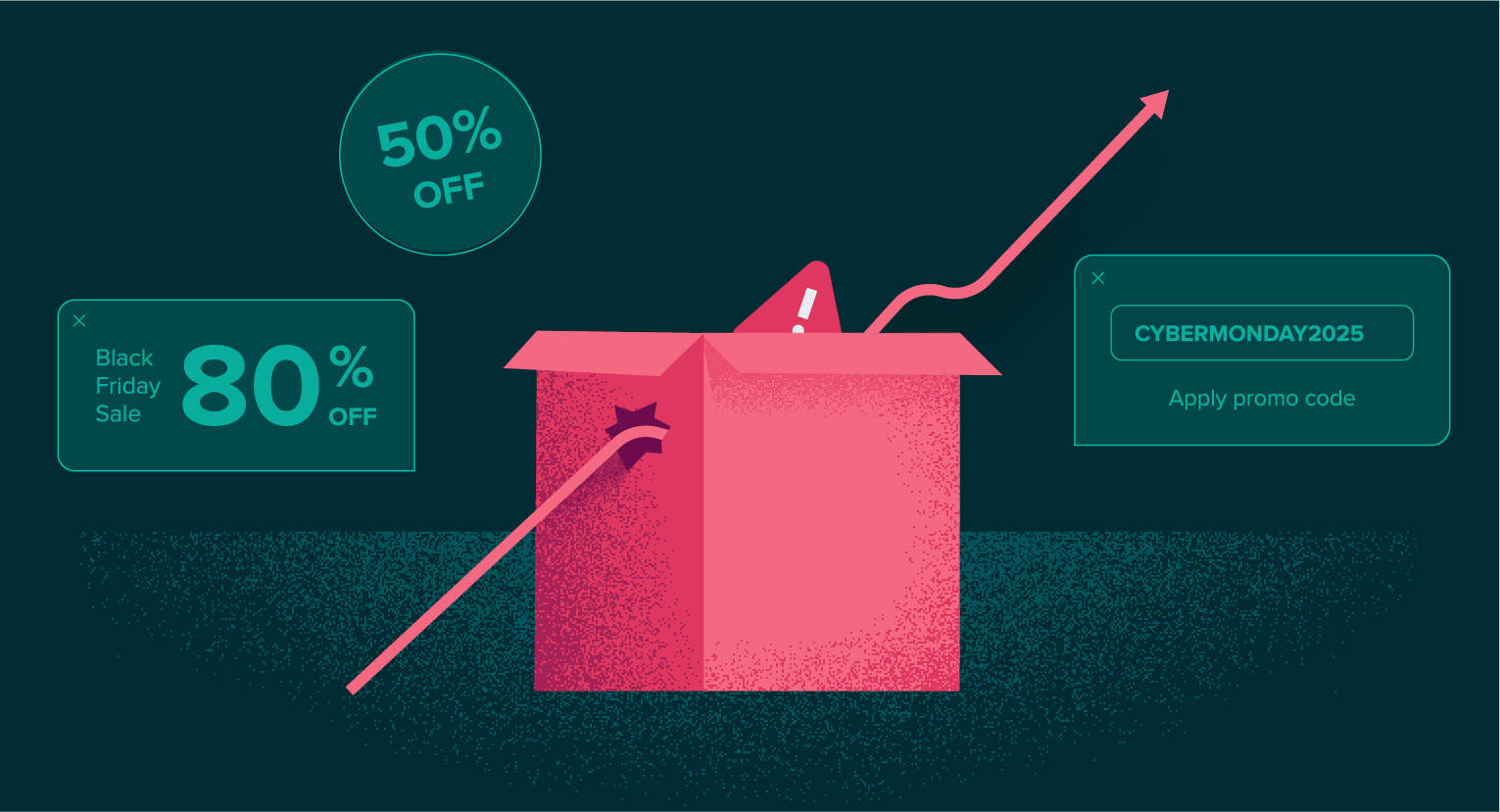
Just in time for NRF 2026: Retail’s Big Show, Riskified has released new insights on a costly post-holiday headache for digital retailers: refund abuse. In addition to the season’s usual flood of gift returns and exchanges, January rings in a surge in refund claims that quietly erodes margins and strains customer service teams at the … Continued
Cyber Week 2025 marked a record-breaking period for ecommerce, with Riskified’s global merchant network experiencing significant growth in Gross Merchandise Volume (GMV) compared to 2024.
The online betting industry is built around speed, volume and global access. Real-time action and instant transactions fuel the excitement that customers love and return for. But that fast-and-furious tempo has also made real-money gaming (RMG) an attractive avenue for organized cybercriminals. Similar to what we see in cryptocurrency, remittance payments and alternative finance, direct … Continued
Fraudsters online are masters of mimicry. They understand which signals and shopping behaviors raise red flags for merchants and work to avoid them by employing strategies that imitate those of legitimate consumers. For example, Riskified observes that fraudsters often combine “safe” physical goods with risky items in a shopping cart, mixing, for example, lower value … Continued