Don’t Let Fraud Rings Run Rings Around Your Business
What dangers do fraud rings pose merchants? Read this blog post for actionable tips to help merchants detect and foil these attacks.
No merchant is immune to the risk of attack from sophisticated fraud rings. And even if you think your eCommerce store is handling that risk well, complacency is a dangerous choice. Threats from fraud rings often arise unexpectedly and the strategies and schemes they use are continuously evolving.
On average, fraud costs merchants 8% of their annual revenue, and fraud rings account for much of the large-scale fraud that merchants encounter. In this post, I examine the dangers posed by fraud rings and provide actionable tips to help businesses detect and foil these attacks.
Getting up close and personal with fraud rings
Fraud rings are coordinated efforts to defraud merchants by paying for goods with stolen credit cards and credentials. They tend to strike big, and have access to technology and resources that are unavailable to solo or less professional fraudsters. While their advanced methods can make their orders look legitimate at first glance, they do leave incriminating clues. Their activity impacts various identifiable factors – the rate of sales of a particular product, the usage of specific payment methods, traffic from certain IP addresses or devices, etc.
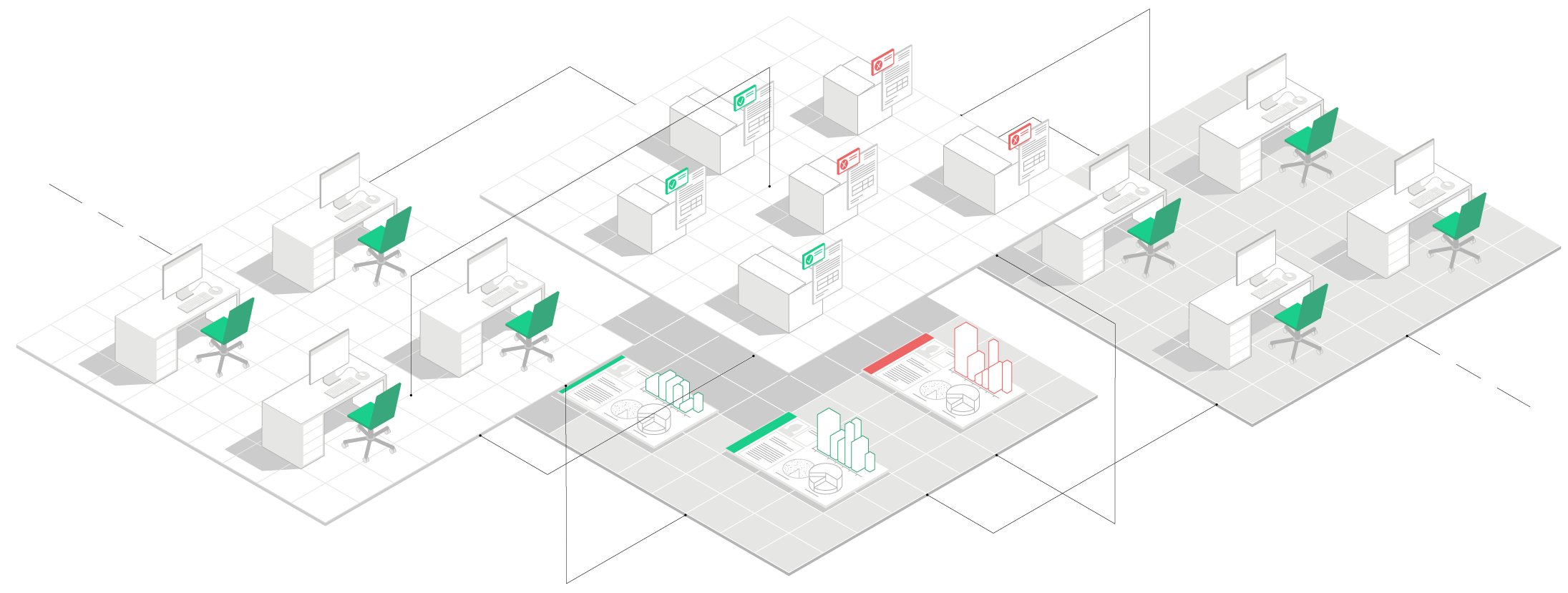
Merchants need to decide whether eCommerce activity that deviates from standard baseline patterns is legitimate, or indicative of fraud. When the activity is repetitive, it’s quite possibly the work of a fraud ring. Detection requires viewing and accounting for a very large number of data points – certainly not a simple task, but there are strategies merchants can undertake to better protect their businesses.
Fraud ring encounters
Riskified has uncovered numerous fraud rings that targeted our merchant partners. Below, we share the modus operandi of three significant fraud rings whose activities we foiled:
The “sim swap” scam
Riskified uncovered a case of a well-known deception, commonly referred to as the sim swap scam, affecting a merchant who was using SMS verifications to confirm their customers’ identities. These orders seemed normal because the billing details matched those of the legitimate cardholder. As it turned out, the fraudsters had contacted phone service providers requesting new sim cards be sent to replace purportedly lost ones. Fraudsters then acquired the ability to verify fraudulent purchases with an SMS authorization.
Riskfied analysts noticed a trend where new customers with new devices were operating customer phones and receiving merchant SMS verifications. We determined that the orders associated with the ring shared several key traits: they were made by first-time customers and were placed using a specific phone carrier and a fairly small and uncommon ISP. By isolating these risk factors, we were able to automatically decline all ensuing fraud attempts without affecting legitimate customer orders.
The “tech support” scam
A sudden spike in the volume and cart value of digital iTunes gift card purchases was picked up by Riskified’s monitoring tools. An inquiry revealed that the majority of these orders were placed by customers over 60 years of age, a consumer demographic that rarely purchases digital iTunes gift cards. Despite the suspicious upturn in volume, many of the customers had previously made legitimate transactions from the same devices, using the same credit cards.
Our analysts suspected this was the work of a sophisticated tech support scam. Fraudsters were contacting their victims over the phone, posing as tech support agents. They informed their victims that they required access to their computers to correct a technical error. When the victims gave them permissions, the fraudster made purchases using the victim’s computer and credit card details.
The “webcam master” fraud ring
Riskified detected a fraud ring which operated through a security breach in D-Link webcams. The fraudsters used webcams both as a means to access computers and as proxies. This provided an IP address that appeared legitimate, and disguised their actual location. The security breach was also used to hack customer accounts. By hijacking the victim’s email the fraudster could re-enter previously accessed merchant sites to order goods.
After noticing some abnormal velocities around certain orders, Riskified detected that all of them were made from a computer with an open port (a TCP or UDP port number that is configured to accept data.) An open port can be explainable, but multiple orders with open ports are rarely coincidental. In addition, the device used to place the order often showed up as a webcam. In fact, registering the devices IP address in any browser address bar led directly to the webcam’s admin interface. Another indicator was that most of the suspicious orders were placed via a Firefox browser. We were able to segment and block transactions with these characteristics, effectively blocking the attack without affecting legitimate shoppers.
Catch em’ if you can!
How can merchants avoid fraud rings? Here are three key tips to help your business detect and foil online fraud perpetrated by organized rings.
Tip 1: Know the characteristics of your real customers
Construct a profile of your typical patron by using data from social networks and online registries (such as WhitePages.com). Become familiar with the age, gender, and geographies that match your online shoppers. This will help you notice irregularities. Knowing that digital iTunes gift cards are not usually purchased by older shoppers was key to detecting the tech support fraud ring.

Tip 2: Link orders to detect anomalies in real-time
Cross-check data from new transactions against previous ones. When the data in a new order matches a previous order it is more likely that the same person has returned to shop at your store. Comparing data will improve your ability to identify anomalies that could be indicative of fraud rings. Some basic elements you may want to keep track of include credit card information, device type, shipping and billing details, IP and email address. Linking will allow you to notice spikes in orders emanating from a certain IP address, or a device/browser/operating system combination.
Tip 3: Build features into your technical fraud detection procedures
Embed analytical insights around unusual behavior and common trends as features in your technical fraud detection process. This ensures that future orders with attributes that stand out will be flagged. For instance, become familiar with the velocity at which your products usually sell per day. If you notice a dramatic and sudden spike in the daily sales of a particular item, an alert will be able to discern between a great day for revenue, or an attack by a fraud ring.

The take-home message on fraud rings
Fraud rings present a real and serious challenge to eCommerce merchants. But adopting some simple strategies can help merchants protect themselves. The key to uncovering these organized rings is the ability to observe and discern anomalies from systematic patterns. By keeping tabs on your customer base and orders, and creating a benchmarking mechanism that sets standard activity ranges, merchants can create a system where unusual activities and velocities will stand out and get the scrutiny they require.
For more information on fraud prevention and managing the threat presented by fraud rings, visit our resource center, or contact us at [email protected]



